Online Virtual Conferences
DFIR - OSINT - CYBER
PFIC is evolving in 2025 with a series of exciting virtual events throughout the year! Each event will feature cutting-edge content relevant to DFIR, OSINT, and Cyber professionals.
Register for one or more events and gain access to online sessions, the PFIC Portal, and valuable networking opportunities. Each event date must be registered for seperately to get access to that virtual event.
ATTENDENCE
Complimentary Enrollment for All!
Our sponsors for PFIC have sponsored enrollment for the event and there is no cost to you to attend any of the virtual events.
Our Sponsors
If you are interested in sponsoring any of the PFIC events please reach out to us a via email.

Paraben Corporation
Paraben Corporation provides digital forensic solutions, with their flagship product being the E3 Forensic Platform. This comprehensive suite empowers investigators to efficiently acquire and analyze data from diverse digital sources, including smartphones, computers, cloud storage, and IoT devices. E3 streamlines digital investigations with its robust features for data acquisition, parsing, analysis, and reporting, catering to law enforcement, government agencies, and private sector professionals.

OSMOSIS
Join the Osmosis Institute and become part of a community dedicated to exploring the frontiers of OSINT.
Connect with like-minded
individuals, researchers, and innovators. Explore the OSC certification for
OSINT investigators. Collaborate with a community of digital investigators.

Cyber Social Hub
Join for FREE & access articles, specialized groups of your interests, informative videos, and a community of other professionals.
ForensicMag
Forensic® (FOR) is the #1 leading source for daily breaking news in the forensic research community. While FOR has evolved over the years since its inception as a former magazine in 2005, FOR continues its unwavering commitment to its loyal readers of forensic and crime scene professionals. Currently, FOR is published daily online and covers a breadth of information vital to forensic professionals - from DNA to trace analysis, sample prep, toxicology, crime scene technologies, and technological advancements across the relatively dynamic and evolving forensic landscape.

PI Magazine
Are you a professional investigator seeking the edge in a constantly evolving field? PI Magazine
is your indispensable resource, delivering unparalleled insights, expert analysis, and cutting-edge strategies directly to your doorstep (or inbox!). For over 37 years, PI Magazine has been the most trusted publication for PIs, committed to educating and informing you with the sole purpose of helping you become the most skilled and successful investigator in the profession.
Each issue is packed with comprehensive and current advice, in-depth articles from seasoned experts, and vital information to help you navigate complex cases, master new technologies, and stay ahead of industry trends.

OSINT Cocktail
Dive into the world of online investigations with the OSINT Cocktail podcast! Join veteran investigators as they dissect films each week, revealing real-world open-source intelligence techniques hidden in plain sight. Learn practical skills in OSINT, digital forensics, fraud investigation, and more, and uncover how to apply these methods to your own inquiries. Tune in and become a more insightful digital investigator!

Sponsorship Available
Limited sponsorship opportunities available for PFIC's leading virtual events. Secure your exclusive virtual booth, access premium lead lists, and gain unparalleled exposure. Don't miss out!
PFIC Summer Agenda
August 20-21, 2025
All times listed are on the Eastern Time Zone.
AUGUST 20th
9:00 AM to 10:00 AM
FBI cell phone location techniquest
SPEAKER
Donald Wochna
This presentation will explore the methodologies employed by the FBI to determine the location of cellular devices. It will cover the range of technologies and legal frameworks involved, including Cell Site Location Information (CSLI), real-time tracking, and cell site simulators. The abstract will examine the varying degrees of precision offered by each technique, the legal considerations surrounding their use, and the evolving balance between law enforcement needs and individual privacy rights.
10:10 AM to 11:00 AM
Hunting the Unseen: Threat Detection and Exploitability in APT TTPs

SPEAKER
Amro Haddadah
As threat actors continually evolve their tactics, techniques, and procedures (TTPs), it’s vital to stay one step ahead in safeguarding critical systems. This session, powered by the expertise of CyberXYZ and leveraging our cutting-edge xyz APT Scanner, delves into the art and science of proactive threat hunting and digital forensics and incident response (DFIR). We will explore adversary emulation through advanced persistent threat (APT) exploitation methodologies, including both exploited vulnerabilities and yet-to-be-exploited findings. Attendees will gain actionable strategies to identify, track, and mitigate threats before they materialize—enhancing their defensive posture with the backing of real-world insights and advanced threat intelligence from CyberXYZ.
11:10 AM to 12:00 PM
Top Tools & Tips to Kickstart Your OSINT Journey

SPEAKER
Ritu Gill
This session provides newcomers with a practical introduction to Open Source Intelligence (OSINT). Participants will gain an understanding of fundamental OSINT concepts and discover key resources for effective data collection, analysis, and verification. The talk will highlight top OSINT tools and best practices to equip attendees with actionable insights for immediate application.
12:10 PM to 1:00 PM
Black Box Investigations: Navigating the Risks of Automated Data Collection

SPEAKER
Jessica Stutzman
This session explores the challenges and risks of relying on black box technologies in OSINT investigations, using real world case studies of evidence being thrown out. Attendees will gain insights into the pitfalls of automated tools, including validation gaps, algorithmic bias, and legal concerns. The session will also highlight how unverified outputs can undermine justice and trust in investigations. Key takeaways include understanding the limitations of black box systems, strategies to balance automation with manual oversight, and best practices for ensuring transparency, accountability, and accuracy in high-stakes investigations.
1:10 PM to 2:00 PM
Utilizing Phone Forensics: Tracing a Device Without an Active SIM to Aid in Locating a Missing Person or Evasive Person of Interest

SPEAKER
Joey Ortega
In high-stakes investigations involving missing persons or elusive suspects,
the absence of a SIM card in a mobile device is often mistaken for the absence
of leads. This presentation challenges that belief. Drawing from field-tested
methodologies and forensic innovation, it reveals how so-called inactive phones
can still produce a trail of digital evidence. Participants will explore how
unique device identifiers like the IMEI continue to interact with wireless
networks, public WiFi systems, Bluetooth sensors, and app-level data storage.
The session will provide a structured process for tracing movement, extracting
location history, analyzing passive network engagement, and deploying tactical
detection tools in real time. This is not just about unlocking devices. It is
about unlocking overlooked opportunities. Investigators will leave with a
sharper understanding of how to turn cold devices into live sources of
intelligence.
August 21st
9:00 AM to 10:00 AM
Real-World Impact: How AI Helped UK Police Fast-Track Riot Evidence Review

SPEAKER
Tom Oldroyd
A deep dive into how the Police Service of Northern Ireland used AI to review over 15,000 video files from UK riot events – a task previously expected to take years. We’ll explore how AI minimised human fatigue, increased accuracy, and reduced operational costs.
Key Takeaways:
AI vs. manual review: What changed
Lessons learned from PSNI
Risks of relying solely on human analysis
10:10 AM to 11:00 AM
Beyond the Database: Revealing Hidden Mobile Evidence in Forensic Investigations

SPEAKER
James Eichbaum
Mobile apps hold a wealth of data, yet critical evidence often lies beyond the main database, overlooked by standard forensic tools. This session explores the vital role of Wrtite Ahead Log (WAL) and Shared Memory (SHM) files in mobile forensics, revealing how they capture uncommitted and deleted data. Attendees will gain practical skills to manually extract, analyze, and validate this hidden evidence, enhancing their investigative outcomes. Through real-world case studies, we’ll uncover how these techniques have solved complex cases by reconstructing app data that automated tools miss. Key takeaways include understanding WAL and SHM file interactions, methods to recover deleted records, and hands-on validation strategies. Join this session to elevate your mobile forensics expertise and uncover the full story behind mobile app evidence.
11:10 AM to 12:00 PM
Exploring WSL Artifacts on Windows

SPEAKER
Hussam Shbib
In today’s increasingly hybrid computing environments, tools that provide Unix-like environments such as the Windows Subsystem for Linux (WSL) are being widely adopted on Windows systems for development, automation, and system administration. While WSL offers powerful capabilities, it also introduces a set of forensic artifacts that digital examiners must be familiar with to recognize and analyze. This session will serve as a forensic crash course - starting with an overview of WSL and progressing into the identification, analysis, and interpretation of key WSL-related artifacts left on Windows systems. As APTs always look for methods to evade detection, understanding the limitations of traditional forensic tools and gaining visibility into WSL activity becomes critical. This session aims to empower DFIR practitioners with the knowledge necessary to uncover traces within hybrid environments and enhance their investigative capabilities.
12:10 PM to 1:00 PM
Embracing Extended Reality in Education

SPEAKER
Peter La Monica
This presentation explores how Manchester Community College (MCC) is pioneering education in Extended Reality (XR) by integrating immersive technologies into its Computer Science curriculum. Launched in Spring 2023, MCC’s XR program is designed to meet the growing demand for XR skills in industries such as healthcare, advanced manufacturing, education, and retail.
1:10 PM to 2:00 PM
AI Prompt Engineering for Investigations

SPEAKER
Greg Kipper
Tired of being buried under mountains of data in your investigations? Feeling like you're spending more time searching than analyzing? Discover how the strategic application of AI prompt engineering can fundamentally transform your investigative processes. This session will reveal how crafting precise and targeted prompts can unlock deeper insights hidden within your data, streamline your analysis workflows, and ultimately lead to faster, more accurate, and more impactful results. Learn practical techniques you can implement immediately to leverage the power of AI for enhanced investigative outcomes.
PFIC Fall
November 12-13, 2025
All times listed are on the Eastern Time Zone.
November 12
9:00 AM to 10:00 AM
Smartphone Forensics Year in Review

SPEAKER
Amber Schroader
Smartphones have transitioned from communication devices to complex repositories of digital evidence.
Their increasing processing power, diverse functionalities (apps, location services,
biometrics), and integration into users' daily lives present both unprecedented
opportunities and challenges for forensic investigations. Every fall we see new
firmwares release and a new evolution to smartphone data. This session will go
through those changes and what to watch for.
10:10 AM to 11:00 AM
All Source Intelligence

SPEAKER
Dr. Nilay Mistry
All-source intelligence analysts collect, dissect, and assess raw data from various sources to ensure the accuracy and optimization of intelligence activities. They also author finished intelligence products that collate information from various sources and disciplines.
11:10 AM to 12:00 PM
Challenging Digital Forensic Testimony in 2025 and beyond
SPEAKER
Donald Wochna
The increasing complexity of digital devices and data presents novel challenges to the admissibility and reliability of digital forensic evidence in legal proceedings. This presentation will explore emerging issues in challenging digital forensic testimony, including the impact of rapidly evolving technologies, the use of artificial intelligence in forensic analysis, and the potential for bias or error in expert interpretation. It will also address legal standards for admissibility, cross-examination strategies, and methods for effectively communicating complex technical information to non-technical audiences.
12:10 PM to 1:00 PM
AI-Powered Digital Forensics: Revolutionizing Incident Response

SPEAKER
Mehul Dubey
The rapid evolution of cyber threats has outpaced traditional digital forensics and incident response methodologies, necessitating innovative solutions to address modern challenges. This paper explores the transformative potential of artificial intelligence (AI) in revolutionizing digital forensics. By leveraging advanced machine learning algorithms, natural language processing, and pattern recognition, AI-powered tools enhance the speed, accuracy, and scalability of evidence analysis, threat detection, and incident reconstruction. We examine real-world applications, such as automated log analysis, anomaly detection, and predictive threat modelling, demonstrating how AI reduces response times and mitigates human error. Furthermore, we address the ethical and technical challenges of integrating AI into forensic workflows, including data privacy, algorithmic bias, and validation of AI-driven findings. This study underscores AI’s role as a force multiplier in incident response, offering a proactive and adaptive framework to combat the growing complexity of cybercrime.
1:10 PM to 2:00 PM
Crypto-agility - Great in Theory, but What About the Real World?

SPEAKER
Samuel Tseitkin
The concept of crypto-agility—the ability to seamlessly swap cryptographic algorithms in response to new threats—has gained significant traction in security discussions. It is often presented as the ideal solution to future-proof systems against quantum computing, evolving cryptanalysis, and unexpected vulnerabilities. However, while the theory is compelling, the reality is far more complex. For most organisations, even a single cryptographic migration is a major undertaking, requiring years of planning, testing, and execution. If migrating from one algorithm to another is already a challenge, how realistic is it to expect businesses to continuously adapt their cryptographic infrastructure?
This topic will examine the practical difficulties of achieving crypto-agility, including legacy system dependencies, regulatory constraints, and operational challenges. Real-world examples, such as the slow adoption of post-quantum cryptography, compatibility issues (such as Google Chrome's attempt to migrate) and the lingering presence of deprecated encryption standards, will highlight how difficult it is to execute even well-planned cryptographic transitions. The discussion will also explore cases where "crypto-agility" has been misunderstood or misapplied, leading to security gaps rather than resilience (such as the SIKE algorithm).
Despite these challenges, crypto-agility should not be dismissed as an impractical ideal. Instead, it must be approached with a clear and structured roadmap that acknowledges the limitations of real-world implementation. This topic will present strategies for designing cryptographic systems with built-in adaptability, focusing on modular architectures, automated update mechanisms, and risk-based transition planning. It will also emphasise the need for solutions that do not simply shift the burden to enterprises but instead make crypto-agility manageable and actionable.
By the end of this paper, recipients will gain a realistic perspective on crypto-agility—what it can and cannot achieve—and leave with practical guidance on how to incorporate it effectively without overpromising or underdelivering.
November 13
9:00 AM to 10:00 AM
Unlocking OSINT: Beyond the Buzzword

SPEAKER
Cynthia Navarro
Join us for a dive into the real world of Open-Source Intelligence (OSINT)—what it is, how it's used across sectors, and why understanding its true potential (and limitations) matters more than ever. We'll cover practical insights on free training options, tools, trusted experts to follow, AI’s growing role (the good and the bad), and resources to sharpen your skills. Whether you're just starting out or refining your craft, this session is packed with actionable takeaways for every level.
10:10 AM to 11:00 AM
Case Study of AI and Incident Response

SPEAKER
Rafael Gorgal
Artificial intelligence (AI) is rapidly transforming the landscape of incident response. By leveraging machine learning, natural language processing, and automation, AI offers significant potential to enhance the speed, accuracy, and efficiency of detecting, analyzing, and responding to security incidents.
This case study explores the application of AI in various stages of incident response, including threat detection and prediction, automated triage and analysis, intelligent containment and eradication strategies, and improved post-incident analysis.
A discussion of the benefits of AI in augmenting human expertise, reducing response times, and ultimately strengthening an organization's security posture in the face of increasingly sophisticated cyber threats.
11:10 AM to 12:00 PM
The Lone Examiner: The Perks and Pitfalls of Going Solo in Digital Forensics

SPEAKER
Stacy Eldridge
In 2019, Stacy Eldridge started her own digital forensics and cybersecurity consulting business. After weathering the challenges of entrepreneurship—and the COVID-19 pandemic—she’s here to share the highs, lows, and hard-earned lessons of going solo. Learn from her mistakes, be inspired by her wins, and gain practical insights into carving out your own path in digital forensics.
12:10 PM to 1:00 PM
Questioning the Expert and their Expert Reports in Adversie Settings

SPEAKER
Larry Leibrock
In most Western National Legal systems we provide digital forensics services and expertise in adverse judicial situations. We should expect rigorous review of ourselves and our work. This is rarely a topic for professional training. This presentation is intended to fill this apparent gap and prepare your for adverse interactions
1:10 PM to 2:00 PM
Crypto Creepers: Unmasking Telegram’s Bitcoin Bandits with OSINT
SPEAKER
Kirby Plessas
This presentation delves into the use of Open Source Intelligence (OSINT) techniques to investigate and expose illicit activities involving Bitcoin within the Telegram messaging platform. As cryptocurrency adoption grows, so does its exploitation by malicious actors. This abstract outlines how OSINT methodologies can be applied to track, identify, and attribute criminal activity, focusing on case studies of individuals or groups leveraging Telegram for scams, fraud, and other Bitcoin-related offenses. Attendees will gain insights into the specific OSINT tools and strategies employed to uncover digital footprints, connect disparate data points, and ultimately unmask the identities and operations of these "Bitcoin bandits."
Speaker Bios
Listed in order of presentation
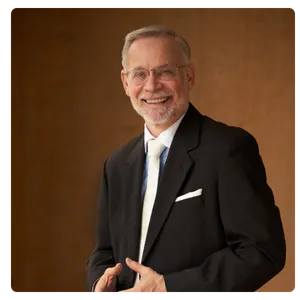
Donald Wochna
Donald Wochna is one of the few attorneys in the United States that is also a certified Computer Forensic Examiner and a Certified Mobile Device Forensic Examiner. He is an Ohio resident, Vietnam Veteran, and former associate at Thompson Hine and partner at Baker & Hostetler, where he practiced after graduating from The Law School at the University of Chicago in 1983. His legal practice strategies and advice in criminal and civil matters combine advanced technical and legal analysis to identify and achieve legal objectives within electronic environments.
He currently provides expert services through Digital Safety Group LLC. DSG provides forensic and data services that help clients and their attorneys achieve objectives with or without confrontation with third parties, including divorce, custody, internal corporate investigations, privacy, stalking, and harassment prevention.

Amro Haddadah
I am the founder of CyberXYZ, where I lead the development of advanced cybersecurity solutions, including the innovative xyz APT Scanner. With over seven years of experience in cybersecurity, I have worked with some of the world’s leading organizations, such as Microsoft, Roche, and SafetyCLI, specializing in threat hunting, DFIR, and defending against advanced persistent threats (APTs).
At Microsoft’s CIRT team, I managed incident responses for major cyberattacks, including SolarWinds and Hafnium, and developed automated investigation tools to streamline threat detection. At Roche, I spearheaded global security operations as Principal Cybersecurity Analyst, implementing Zero Trust architecture and AI-driven threat detection. Currently, as Lead Cybersecurity Researcher at SafetyCLI, I oversee enterprise security architecture, vulnerability analysis, and machine learning applications in threat detection.
My expertise spans cloud security, post-exploitation techniques, and APT methodologies, and I am committed to driving innovation and empowering organizations to stay ahead of emerging cyber threats.

Ritu Gill
Ritu Gill is an Open Source Intelligence (OSINT) Analyst with over 17 years of experience working with Canadian law enforcement. She is a recognized subject matter expert (SME) in OSINT. After serving 12 years with the Royal Canadian Mounted Police (RCMP), Ritu launched a consulting business specializing in OSINT training and research for law enforcement and related organizations across North America. Ritu is also the President of OSMOSIS, an organization dedicated to standardizing OSINT practices and connecting professionals in the field. Ritu holds a Bachelor's Degree in Criminology and remains an active member of the OSINT community.

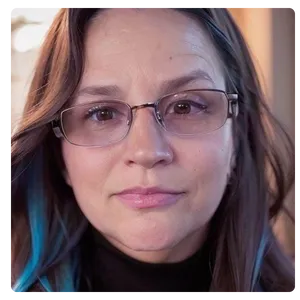
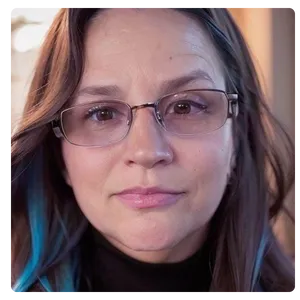
Jessica Stutzman
Jessica Stutzman is the founder and president of Pangea Research LLC, a specialized investigative consultancy focused on OSINT, digital footprint analysis, and reputational risk research. A U.S. Army veteran and seasoned investigator, Jessica supports law firms, government agencies, and international organizations in high-stakes civil, criminal, and internal matters. She is a doctoral candidate in Strategic Intelligence and serves as an OSINT expert with the United Nations, where she contributes to global investigations and digital threat assessments. Her academic research centers on human-in-the-loop processes in PAI-based investigations, with a focus on improving accuracy and reducing error in digital suspect identification. Jessica is known for her forensically sound methodologies, legal-grade documentation, and deep experience training law enforcement and intelligence professionals. She brings rigorous analysis, contextual judgment, and a truth-driven approach to every engagement, bridging digital tradecraft with real-world operational needs.

Joey Ortega
Joey Ortega began his investigative career at 18, working as an apprentice investigator specializing in insurance fraud and background checks. Demonstrating exceptional skill in surveillance and information gathering, Joey quickly advanced to tackle increasingly complex cases. He transitioned to conducting internal investigations for major companies like Sears, Roebuck & Co., Saks Fifth Avenue, and Kmart, uncovering internal theft, embezzlement, and organized crime. His success led to a national investigator role for a cellular retail chain, managing crime ring investigations on a national scale. Trained in the Reid Technique for interviewing and interrogation, Joey consistently secured confessions without any prosecution challenges. While working for private investigative agencies, he expanded into defense investigations, missing persons cases, and stalking investigations. His work in stalking cases sparked a passion for cyber-crime, where he mastered tracking harassing emails and became a trusted resource for victims of internet fraud and cyberattacks. His innovative methods in tracking eBay fraudsters were featured in PI Magazine in June 2005. Joey’s investigative journalism further enhanced his expertise in OSINT (Open-Source Intelligence), HUMINT (Human Intelligence), SOCINT (Social Media Intelligence), and GEOINT (Geo-spatial Intelligence) applying these skills to high-profile cases involving criminal networks, cyber-crime, and corporate espionage.

Tom Oldroyd
An ex-Sergeant from Nottinghamshire Police of 17 years, Tom managed a standout Digital Forensics Unit in the UK before hanging-up his cuffs to work in Apple Forensics with BlackBag Technologies, part of Cellebrite, and he now leads S21’s strategy and sales activities for Semantics 21.

James Eichbaum
James Eichbaum is a retired law enforcement officer with 16 years of experience, having served as a Detective with the Modesto Police Department and Stanislaus County Sheriff's Office in California. He worked with the Sacramento Valley High Tech Crime Task Force and as a Special U.S. Deputy Marshal with the FBI Cyber Crimes Task Force. A digital forensics expert with over 1,000 hours of training, James holds a Bachelor’s in Information Systems Security and Associate degrees in Computer Science and Criminal Justice. His expertise shone in a 2011 murder and arson case, earning him the HTCIA Case of the Year Award for recovering deleted messages, later featured in TV documentaries. For 14 years, James has delivered advanced training in mobile device forensics, specializing in extraction methods, app analysis, SQLite forensics, and Python scripting, equipping professionals to tackle modern digital evidence challenges.

Hussam Shbib
Husam Shbib is a professional cybersecurity consultant,
adept in penetration testing, digital forensics, malware analysis, programming,
and OSINT. Throughout his career, he has exhibited an unwavering commitment to
overcoming challenges, considering them stepping-stones to success.
He is the founder of the MemoryForensic website, a valuable resource for
learning about digital forensics, especially memory forensics.
He holds multiple well-regarded cybersecurity certifications, including ICMDE,
CCE, CCD, CCDFA, 13Cubed IWM, 3CE, 3CI, eCDFP, MCFE, etc. These certifications
underscore his commitment to maintaining a high level of expertise and staying
current with industry’s best practices.
He is also a speaker at well-known conferences and events such as BlackHat MEA,
ASFSFM, IBA Karachi University, 3D Forensics, etc.
He is an advocate for fostering awareness in cybersecurity communities. So, he
is committed to sharing cybersecurity knowledge, both through online platforms
such as LinkedIn and YouTube, as well as online & in-person mentoring.

Peter La Monica
Peter La Monica is an Associate Professor and Chair of the Computer Science Department at Manchester Community College, where he has been a full-time faculty member since 2012. With over 40 years of teaching experience in academic and corporate settings, Mr. La Monica brings deep expertise in cybersecurity, extended reality (XR), and digital forensics.
Before entering academia full-time, Mr. La Monica served as a Computer Forensic Analyst for the United States Postal Inspection Service (USPIS), where he was a pioneer in mobile device forensics. He provided critical support to federal, state, and local law enforcement agencies, assisting in over 400 forensic investigations involving computers and mobile devices—many of which focused on crimes against children, mail fraud, and cybercrime.

Greg Kipper
Gregory Kipper is a futurist and strategic forecaster in emerging technologies. He specialized in IT security and information assurance for 20 years, working for the last 11 years in the fields of digital forensics and the impacts emerging technologies have on crime and crime fighting. Mr. Kipper has been the keynote speaker at select industry events, a digital forensics instructor, and a trusted advisor to both the government and commercial sectors. He has published books in the fields of digital forensics and emerging technologies, including: "Investigator's Guide to Steganography," "Wireless Crime and Forensic Investigation," and "Virtualization and Forensics."

Amber Schroader
For 30 years, Ms. Schroader has been a leading innovator in digital forensics. She's developed software to recover data from various sources, including smartphones, hard drives, cloud storage, email, and even gaming systems. Her expertise extends to creating protocols for evidence seizure and processing, used by organizations worldwide.
Ms. Schroader's vision extends beyond specific tools. She's championed a "360-degree approach" and "Forensics of Everything (FoE)," emphasizing the importance of considering the complete picture of digital evidence. This influential perspective has pushed the field towards a more holistic approach.
Her contributions go beyond software. Ms. Schroader is an accomplished instructor, having written and delivered numerous courses in this specialized field. She's even founded certifications, further solidifying her role in shaping the digital forensics landscape. Her passion continues through industry talks and book contributions.

Dr. Nilay Mistry
Dr. Nilay Mistry is a senior and founding faculty member in Digital Forensics and Cyber Security at the National Forensic Sciences University (NFSU), Gandhinagar, where he currently heads the Centre of Excellence in Digital Forensics (CoEDF) and actively contributes to advanced research, investigations, and capacity-building. Holding a Ph.D. in Digital Forensics from NFSU, along with M. Tech and B.E. degrees in Computer Science and Engineering, Dr. Mistry has delivered specialized training to numerous national and international law enforcement and defense agencies and advises on the development of digital forensic laboratories. His extensive research interests include various areas of digital forensics and intelligence, reflected in his numerous publications, two patents, and over 50 professional certifications. Notably, he played a pivotal role in establishing both the CoEDF and the Cyber Defence Centre (now CoECS) at NFSU, transforming them into leading centers for research and training. Additionally, Dr. Mistry serves on government expert committees and is an appointed Examiner of Electronic Evidence under the Information Technology Act, 2000.

Mehul Dubey
Mehul Dubey is a cybersecurity professional specializing in digital forensics, OSINT, penetration testing, and threat intelligence. With 1.6+ years of experience, he has worked on DFIR investigations, cyber risk management, and ISO 27001 compliance at PINAK INFOSEC PVT LTD.
A Certified Ethical Hacker (CEH) and ISO 27001 Lead Auditor, Mehul has spoken at events like National Science Day 2025 at SAGE University, sharing insights on digital forensics in cybersecurity. His passion lies in investigating cyber threats, leveraging AI-driven security solutions, and educating the cybersecurity community.

Samuel Tseitkin
Samuel is a passionate advocate for emerging technologies, with a strong foundation in AI and cybersecurity. During his university years, he co-founded the Artificial Intelligence Student Society (AISSOC), a hub for students collaborating on AI projects, where he contributed to multiple initiatives.
After completing his Cybersecurity studies at Monash University, Samuel became deeply interested in quantum computing and its implications for digital security. Recognising the urgent need to adapt cybersecurity strategies for a post-quantum world, he founded ExeQuantum to not only raise awareness of the quantum threat but also provide cutting-edge cryptographic solutions.
Since then, Samuel has established himself as a thought leader in quantum-resistant cybersecurity, delivering lectures, leading panels, and driving discussions across top innovation and technology hubs, including Stone & Chalk, the University of Melbourne, Swinburne University and Melbourne Python. His mission is clear: to ensure businesses and institutions are prepared for the next era of digital security.

Cynthia Navarro
Ms. Navarro is a licensed California Private Investigator and principal of Finnegan’s Way; an investigative consultation and training firm located in California. She has been in investigations for over 40 years. Most recently she is President Emerita, of OSMOSIS, an association for open-source professionals who support the development of the OSINT tradecraft. Prior to Finnegan’s Way, Ms. Navarro held various management positions at several Silicon Valley companies. Throughout her career, Ms. Navarro has been responsible for managing business intelligence gathering, intellectual property theft, interviews, cyber investigations, background investigations, and training. She has taught using the internet as an investigative tool (OSINT) to thousands of law enforcement and investigators worldwide. Ms. Navarro was President of the High Technology Crime Investigation Association and held many positions for the Silicon Valley Chapter. She holds a B.S. in Criminal Justice from California State University – East Bay.

Rafael Gorgal
Rafael Gorgal, is a highly experienced digital forensics and information security consultant, and served three terms as past President of the Southwest Chapter, High Technology Crime Investigations Association. With over 20 years of experience as an Expert Witness in court testimony, he has conducted numerous forensic investigations, developed incident response methodologies, and managed forensic consulting teams, in addition to creating computer forensic curriculums for both private sector and law enforcement investigators. His extensive consulting work in information systems security includes network vulnerability assessments, high technology crime investigation, and cyber-terrorism, notably advising the Office of the Secretary of Defense on information systems security protection programs and pioneering private sector open-source intelligence initiatives for national security and emergency response communities. Mr. Gorgal has taught Information Security at Southern Methodist University, the University of California at Los Angeles, and National Technological University, and is a frequent speaker at security seminars and industry conferences such as InfowarCon and the Paraben Forensic Innovation Conference. He has authored numerous articles on digital forensics, artificial intelligence, blockchain technology, information warfare, and security management, and is a contributing author to the best-selling book series, "Hacking Exposed – Computer Forensics, Secrets and Solutions."

Stacy Eldridge
Stacy Eldridge, a leading cybersecurity expert and the driving force behind Silicon Prairie Cyber Services LLC, offers services in digital forensics, litigation support, and expert witness testimony. A former Senior Forensic Examiner with the FBI's Computer Analysis Response Team for nearly a decade, Stacy contributed to significant cases, including the first conviction for material support of terrorism, and developed forensic training programs. She further honed her expertise at General Electric, building their data loss prevention program, and at Lincoln Electric System as Director of Cyber Security, protecting critical infrastructure. Stacy holds multiple certifications (GSEC, GCCC, GCFE, ACE, CFCE) and a Master of Science degree, and is a Licensed Private Detective. Passionate about understanding and explaining digital evidence, she also teaches at renowned institutions and coaches for IACIS.

Larry Leibrock
Larry Leibrock is a cyber professional of over thirty years at the intersection of technical intelligence collection, forensics analysis, cybersecurity, and teaching. He has taught at the Idaho National Laboratory and works as a private investigative digital forensics consultant. He holds a Ph.D, DA, and MBA, and certifications including CISSP and NSA IAM. He has a wide range of expertise includes cyber-enabled investigations, incident response, cyber threat intelligence, digital forensics, analytical pathologies in intelligence analysis, and resilience models for complex systems architectures.
Kirby Plessas
Kirby Plessas is founder and CEO of Plessas Experts Network, Inc. Before devoting her work full time to PEN, Kirby established herself as one of the foremost tradecraft experts in OSINT through successful careers both as a member of the U.S. Military and as a contractor prior to founding PEN in 2008.
A service-disabled veteran, Kirby began her career in Military Intelligence as an Arabic linguist supporting the Department of Defense. Upon completion of her Army service, Ms. Plessas complemented her MI expertise through utilizing her OSINT experience at the Defense Intelligence Agency to support the warfighter as well as supporting other Intelligence Community activities. Acknowledged as an expert in her field, in 2007 she was selected to participate and instrumental in the creation and institution of an innovation center for conducting OSINT. In great tribute to her long list of personal and corporate accomplishments in her field, DHS declared Kirby Plessas an OSINT Technical Expert (2010). Through her work at PEN, Kirby shares her love of innovative technology and OSINT expert skill through corporate workshops as well as consulting and delivering hands-on training courses.
Why should you attend PFIC...
Why should you attend PFIC...
“If you have not looked at attending the Paraben Forensic Innovation Conference you should. The DFIR event has great talks and lots of hands-on lab tracks. Even though the conference is called Paraben, there are a lot of other forensic companies there. And, you can talk to lots of real users. Unlike other conferences that cost thousands, this digital forensics conference is affordable for any budget.”
Ira Victor, Chief Forensic Analyst
“I was extremely pleased with the incredible professional level of speakers throughout this forum. The information they provided was extremely valuable. Throughout both my police career and digital forensics, I would rate this forum at the very top. PARABEN did an excellent job.”
James Bogers MJB group
“OMG. I learned so much in the first hour of PFIC my mind is blown. As you may or may not be aware, I have been in investigations for over 35 years. I speak internationally on Police Policy and Procedure INVESTIGATIONS. I have NEVER at least that I Can recall, learned so much in one hour! This is such an incredible journey.”
Frank DeAndrea DeAndrea Investigations